Updated on 2026-02-11
views
5min read
The Digital Archaeologists of a Changing Era
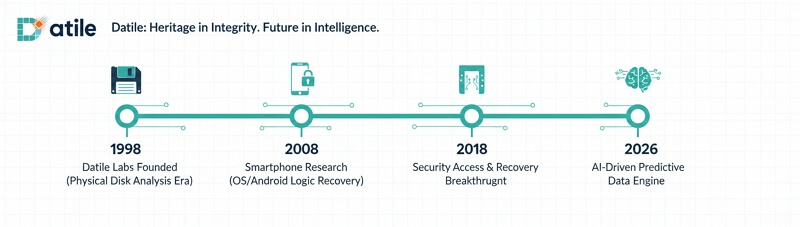
In 1998, the digital world was a landscape of dial-up modems, the rhythmic hum of mechanical hard drives, and the fragile reliability of 1.44MB floppy disks. It was in this formative year that Datile was established. At that time, "data recovery" was a niche craft—a meticulous surgery performed in cleanrooms to rescue fragments of information from failing magnetic platters.
Fast forward twenty-seven years, and the digital fabric of human life has undergone a total metamorphosis. We have transitioned from tangible, clanking hardware to the ethereal complexity of cloud-integrated ecosystems and encrypted silicon. Yet, throughout this nearly three-decade journey, one constant remains: the vulnerability of human data.
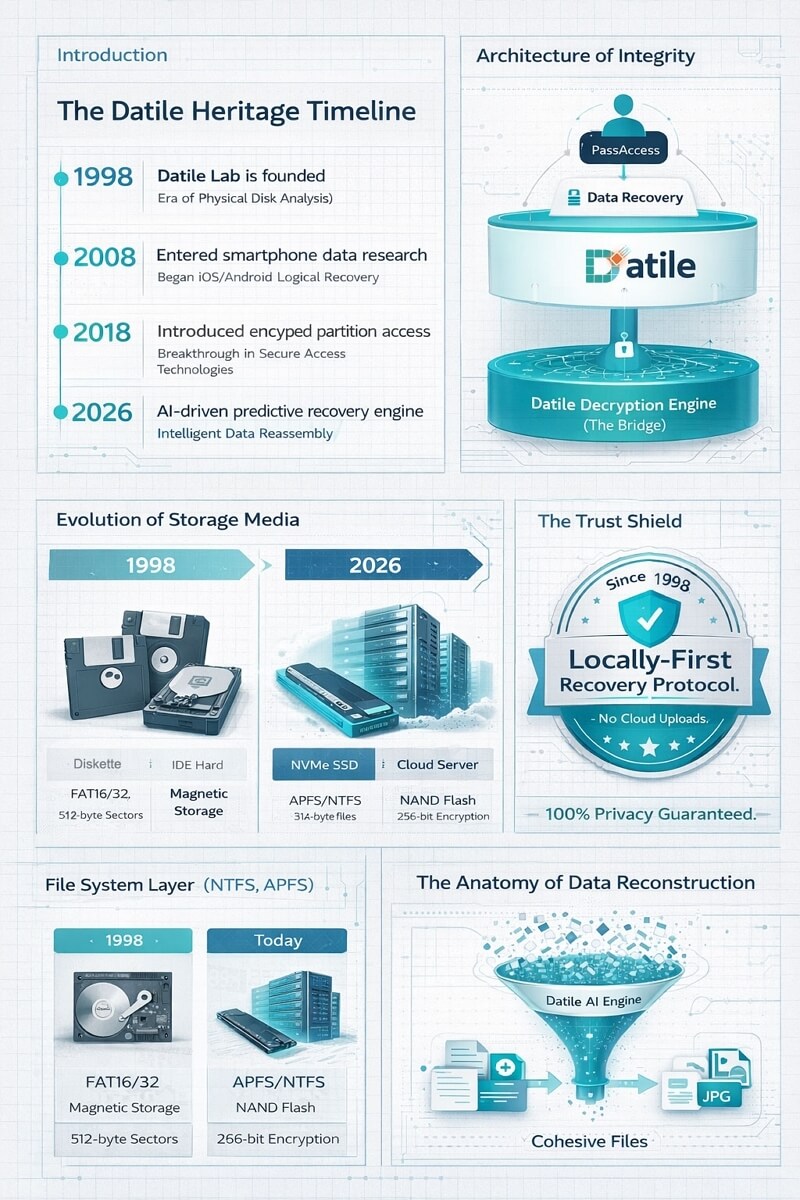
As one of the industry's longest-standing sentinels, Datile has occupied a front-row seat to this evolution. Our domain history is more than just a timeline; it is a repository of the internet's structural shifts. We have evolved from analyzing early FAT16 file systems to engineering AI-driven engines capable of reconstructing lost memories from the most sophisticated encrypted environments.
In this retrospective, we bridge the gap between the legacy and the future. We explore how data recovery has transformed from a mechanical necessity into a high-stakes battle of algorithms—and how Datile’s heritage in digital architecture and data integrity continues to define the gold standard for accessibility and recovery in 2026.
1998–2005—The Precision Surgery of the Mechanical Era
Rescuing Digital Memories from Tracks and Sectors
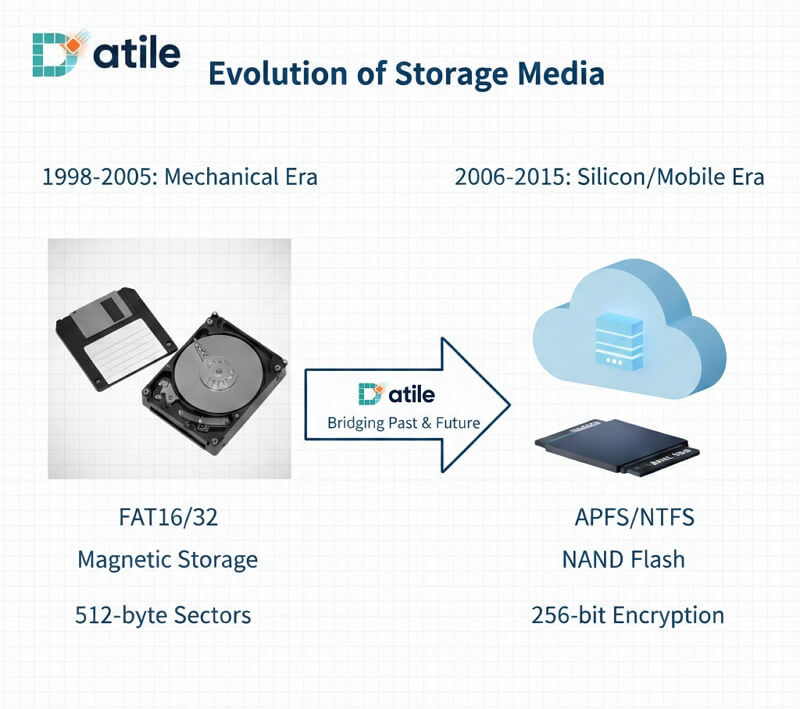
In the early days of the Datile laboratory, data recovery was a high-stakes game played against the laws of physics. In an era where terabyte storage was a distant fantasy, mainstream hard drives peaked at just a few gigabytes. Data did not exist in the ethereal cloud; it was magnetized onto metallic platters spinning at thousands of revolutions per minute.
1. Industry Benchmarks: Technical Boundaries of Early Storage Architecture
To appreciate the challenges of this era, one must examine the limitations of late-90s storage. Datile established industry-leading repair standards through deep-level research into early file systems.
| Technical Dimension | Early HDD Era (1998–2005) | Datile’s Technical Response |
|---|---|---|
| Storage Media | Magnetic Platters (Physical) | Established Class 100 Cleanrooms for physical recovery |
| File System | FAT16 / Early FAT32 | Developed binary cluster analysis tools |
| Addressing Mode | CHS (Cylinder/Head/Sector) | Pioneered transition to LBA (Logical Block Addressing) algorithms |
| Interface Standard | IDE / ATA-3 | Built custom bus adapters to bypass BIOS limitations |
| Common Failures | Head Crashes & Motor Seizures | Developed specialized head-stack replacement protocols |
2. The Datile Insight: The Symbiosis of Physical Decay and Logical Collapse
Between 1998 and 2002, most service providers treated physical repair (hard failure) and software recovery (soft failure) as entirely separate disciplines. However, Datile’s research into tens of thousands of cases led to a prophetic insight:
The Datile Insight: "Microscopic physical degradation triggers a chain reaction at the logical layer. A 'bad sector' is not just a physical spot; it causes fragmentation of the File Allocation Table (FAT) metadata, rendering traditional software tools useless."
Based on this insight, Datile established a rigorous "Cross-Layer Recovery" logic chain:
- Physical Stabilization: Instead of extracting files directly from a failing drive, Datile utilized hardware emulators to create a bit-for-bit Sector-level Image.
- Metadata Reconstruction: To solve the "Orphaned Cluster" problem common in FAT32, Datile developed the "Recursive Logic Tree" algorithm. This bypassed damaged boot sectors to reverse-engineer directory structures based purely on file header signatures.
- The Result: This logic ensured that even in the final minutes before a drive's motor failed permanently, the most critical structured data was prioritized for extraction.
3. Typical User Scenarios: Datile’s Research & Methodology
In the early age of personal computing, users faced highly specific technical hurdles. Datile developed its core methodologies by addressing these recurring pain points:
| Typical User Scenario | Datile’s Research Focus | Applied Methodology |
|---|---|---|
| The "Click of Death" (Mechanical Racket) | Identified as head-stack misalignment or platter scoring. | Cleanroom Head Swap: Replacing damaged actuators in a sterile environment combined with Service Area (SA) firmware repair. |
| Accidental FORMAT Command | Realized data is not erased; only the Root Directory Area is cleared. | Raw Sector Scanning: Ignoring OS errors to scan the entire disk space for known hexadecimal file signatures (Magic Bytes). |
| Unreadable Floppy Disks (CRC Errors) | Addressed magnetic coating decay or mold causing checksum failures. | Intelligent Retrial Algorithm: Developed high-tolerance drivers to re-read sectors and use redundancy logic to fill missing bits. |
| HDD Not Recognized by BIOS | Diagnosed as PCB burnout or Firmware Overflow. | ROM Chip Swapping: Extracting original firmware chips and migrating them to matching donor boards with calibrated servo parameters. |
Through these seven years of foundational work, Datile did more than just recover billions of documents and photos; we established a Fundamental Methodology of Data Integrity. Our profound understanding of the relationship between physical sectors and logical partitions created the bedrock for our future breakthroughs in encrypted mobile systems and AI-integrated reconstruction.
2006–2015—The Mobile Revolution and the Encryption Paradox
Navigating the Shift from Mechanical Platters to Silicon Gates
As the mid-2000s approached, the landscape of data storage underwent a seismic shift. The clatter of mechanical hard drives began to fade, replaced by the silent, rapid-fire processing of NAND Flash memory and the explosive rise of the smartphone. This era redefined the very definition of a "lost file," moving the battlefield from mechanical engineering to complex computational forensics.
1. The Technological Frontier: Silicon Takes Center Stage
The emergence of the iPhone in 2007 and the subsequent Android surge moved the world’s most precious data from desktop towers to the palms of our hands. Simultaneously, Solid State Drives (SSDs) began replacing HDDs in professional workstations. Unlike the predictable magnetic tracks of the past, data was now stored in microscopic electron traps. This transition introduced the industry’s most formidable adversary: the TRIM command.
In traditional HDDs, "deleted" meant "hidden." On an SSD or a smartphone’s internal storage, the TRIM command proactively wiped data blocks to maintain write speeds, making traditional "undelete" methods obsolete overnight.
2. The Greatest Challenge: The "Black Box" of Hardware Encryption
As mobile devices became repositories for our entire lives, manufacturers introduced system-level hardware encryption. For Datile, the greatest challenge of this decade was the Hardware-Software Lock. Recovering data was no longer just about reading bits; it was about negotiating with encrypted kernels and secure enclaves.
Datile’s Breakthrough Logic: Instead of attempting to "break" the encryption—which was computationally unfeasible—Datile shifted its focus to Native Environment Emulation. We realized that the data was only accessible through the device's own logic gates.
- The Breakthrough: We developed a proprietary Low-Level Extraction Bridge. By communicating directly with the NAND controller while bypassing the OS-level restrictions, we could "trick" the hardware into a diagnostic state.
- The Result: This allowed Datile to extract a "Physical Image" of the encrypted chip, which could then be processed through our growing database of decryption keys and system signatures.
3. Professional Depth: SQLite and the Art of Fragment Reconstruction
With the rise of mobile apps, the way data was structured changed fundamentally. Files were no longer simple independent entities; they were entries in a SQLite database (the backbone of iOS and Android).
When a user deleted a WhatsApp message or a photo, the SQLite record was marked as "Free," but the data fragments remained scattered across the NAND Flash cells. Datile pioneered the Heuristic SQLite Parser, a tool designed to scan the unallocated space of a mobile dump to find "orphaned" database pages. By identifying the unique headers of SQLite tables, we could reassemble chat histories and metadata even after the main database had been corrupted or "wiped."
4. Generational Shift: Mechanical vs. Silicon Data Recovery
To illustrate the complexity of this transition, the following table compares the foundational differences between the HDD era and the burgeoning Mobile/SSD era.
| Dimension | Mechanical Era (1998–2005) | Silicon/Mobile Era (2006–2015) |
|---|---|---|
| Typical Scenario | Motor failure, dropped drive, corrupted FAT32 tables. | Accidental factory reset, forgotten passcodes, "Security Lockout." |
| Primary Challenge | Physical mechanical alignment and dust contamination. | Encryption and the TRIM Command clearing data blocks. |
| Datile’s Solution | Cleanroom head replacement and magnetic imaging. | NAND Protocol Extraction and SQLite Fragment Parsing. |
| Data Persistence | High; data remained until physically overwritten. | Low; data is proactively purged by the OS controller. |
| Technical Difficulty | High (Requires manual dexterity and hardware tools). | Extreme (Requires reverse-engineering and forensic logic). |
5. Mobile Forensics: The Birth of a New Discipline
By 2015, Datile had transformed from a hardware repair shop into a Mobile Forensics powerhouse. We understood that in the world of silicon, the physical chip was merely a shell; the true recovery happened within the logic of the NAND Flash controller. Our ability to reconstruct data from the internal SQLite structures of a locked iPhone or a bricked Android device set the stage for our next major evolution: integrating Artificial Intelligence to handle the sheer volume of fragmented digital life.
2016–2023—The Cloud & Security Paradox
Deciphering the Era of Hyper-Encryption and Integrated Ecosystems
By 2016, the digital landscape had reached a state of "Hyper-Encryption." With the introduction of the Apple File System (APFS) and the mandatory integration of iCloud and Google Drive, data recovery was no longer a matter of simply finding bits on a chip. It became a sophisticated negotiation with the "Security Paradox": how to protect user privacy while ensuring that legitimate owners do not lose their digital lives forever.
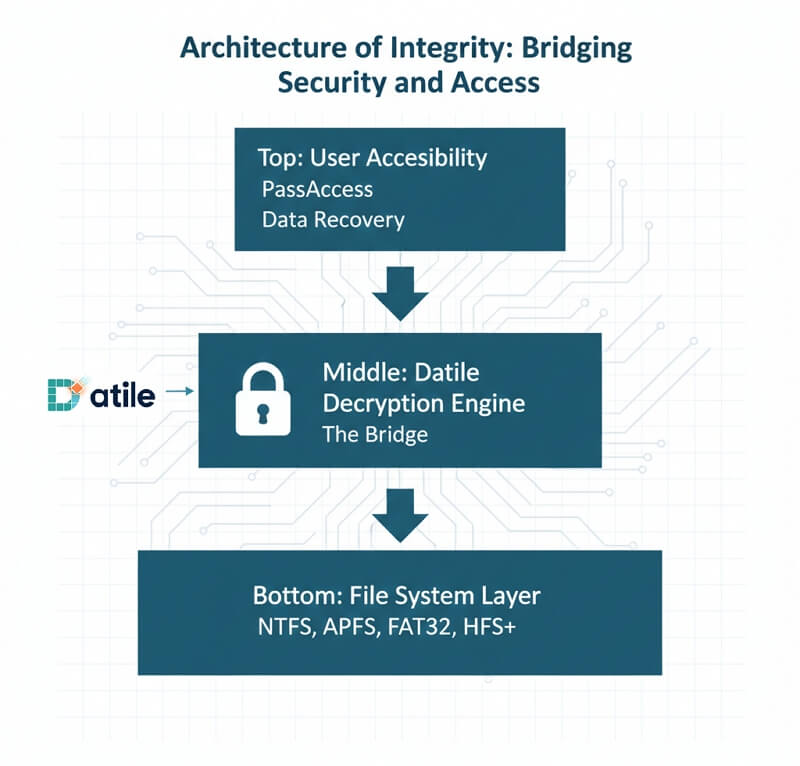
1. Technical Background: The Rise of Secure Enclaves and APFS
During this period, the storage paradigm shifted from local hardware to "Ecosystem-Synced Data." Apple introduced APFS, featuring revolutionary multi-key encryption and "snapshots," while Android implemented File-Based Encryption (FBE) by default.
Devices were now protected by dedicated hardware security modules—like Apple’s T2 and Secure Enclave—which isolated sensitive credentials from the main processor. While this significantly enhanced security, it created a "Digital Deadlock" for users who lost their credentials due to system failures, trauma-induced memory loss, or legacy access issues.
2. The Greatest Challenge: The "Security Deadlock"
The industry faced a crisis: if a device was stuck in a "Security Lockout" or an "Unavailable" state, traditional forensic imaging was useless because the data remained encrypted behind a hardware-locked gate. For Datile, the challenge was to develop a method that respected modern security protocols while providing a path for Accessibility Recovery.
Datile’s Breakthrough Logic: The "Non-Destructive Protocol Bridge" We realized that forcing a "backdoor" was not only unethical but technically impossible with modern hardware. Instead, Datile’s R&D focused on Environment Reconstitution.
- The Research: We studied the way system firmware interacts with the Secure Enclave during boot-loop and lockout states.
- The Breakthrough: Datile developed a proprietary Direct-to-Kernel (D2K) Communication Layer. This allowed us to stabilize the system's firmware environment, enabling the legitimate hardware to perform its own decryption under our diagnostic supervision.
- The Result: This gave birth to the PassAccess technology—a solution that restores device accessibility without destroying the hardware’s underlying security integrity.
3. Market Comparison: Confronting the "Digital Deadlock"
In this era, users found themselves caught between high-cost professional labs and risky "one-click" online tools. Datile positioned itself as the professional, secure alternative.
| Problem Scenario | Standard Market Approach | Datile’s Professional Method | Datile’s Advantage |
|---|---|---|---|
| Forgot Screen Passcode / "Unavailable" Screen | Factory Reset (Wipes all data permanently). | Secure Access Reconstitution (Resets the access path via firmware layer). | Regains device utility without permanent hardware "bricking." |
| System Stuck in Boot Loop (APFS Error) | Restore OS (High risk of overwriting data snapshots). | APFS Snapshot Extraction (Isolates and restores previous system states). | Preserves the file system hierarchy and original metadata. |
| Forgotten Apple ID / iCloud Credentials | Third-party "Bypass" (Unstable, breaks system updates). | Token-Level Association Reset (Cleanses the local device linkage). | Ensures a clean, updateable, and factory-standard system. |
| Multiple Failed Login Attempts | Permanent Device Lock (Requires logic board replacement). | Security Delay Bypass (Safely resets the lockout timer at the kernel level). | Zero hardware modification; keeps the original device serial and warranty. |
4. Professional Depth: APFS Snapshots and Localized Privacy
The move to APFS introduced the concept of "Copy-on-Write" and "Snapshots." Datile pioneered tools that could read these hidden snapshots—temporary versions of the file system stored deep within the NAND memory. Even if a user "deleted" a file or "updated" an OS that crashed, Datile’s Snapshot Recovery Engine could roll back the logical view of the drive to a point in time where the data was still intact.
Furthermore, realizing the sensitivity of cloud-synced data, we committed to the Local-Only Processing Standard. Despite the "Cloud Era," Datile’s tools were engineered to process all decryption and recovery on the user’s local machine, ensuring that private tokens and keys never touched our servers.
5. Transition to Accessibility: The Logic of PassAccess
By the end of 2023, Datile had successfully bridged the gap between Data Recovery and Access Recovery. We understood that in a world of integrated ecosystems, "losing data" and "losing access" were the same thing. This period of research was the final stepping stone toward our current mission: using AI to predictively solve access hurdles before they become permanent digital losses.
2024–2026—The Intelligence Frontier
Generative AI and the Era of Predictive Data Reconstruction
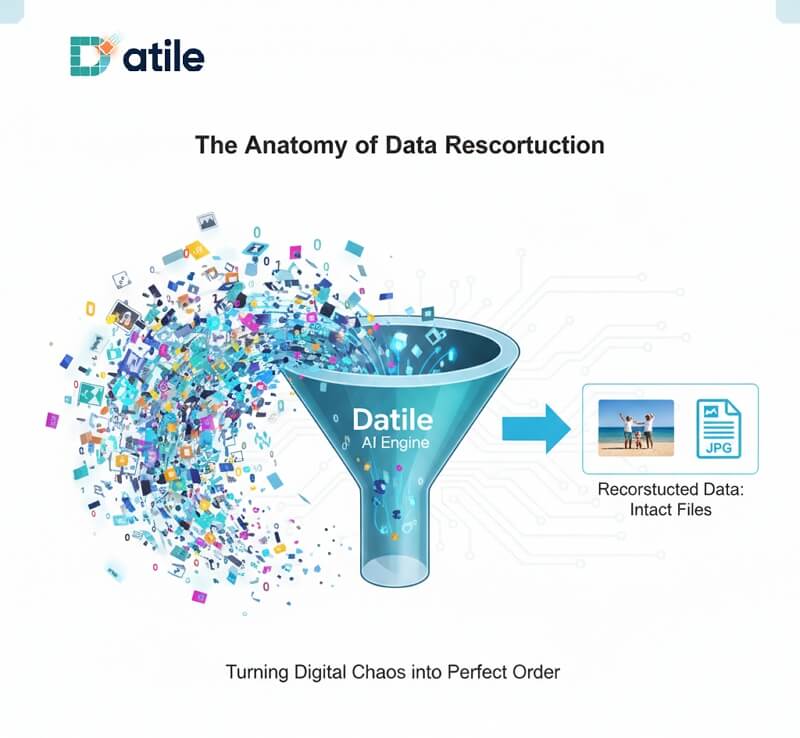
As we move through 2026, the data recovery landscape has transcended the boundaries of manual forensics. We have entered the era of Generative AI Recovery, where Artificial Intelligence is no longer a peripheral utility but the very engine that powers deep-level Heuristic Scanning and Pattern Recognition. At Datile, we are harnessing these neural networks to solve the "Metadata Gap"—recovering what was once considered "noise."
1. Technical Background: AI as the Engine of De-fragmentation
For decades, the "holy grail" of data recovery was the reconstruction of files when the file system's "map" (Metadata) was destroyed. In the past, without metadata, a file was just a series of disconnected 0s and 1s. Today, AI has transformed de-fragmentation from a rigid search for headers into a fluid, predictive process. By analyzing data streams at the sub-sector level, AI can now "understand" the DNA of a file, predicting how fragmented blocks should be stitched back together with near-perfect accuracy.
2. The Datile Innovation: The AI-Driven Data Reconstruction (ADR) Engine
Datile’s latest ADR Engine represents the pinnacle of our 27-year heritage. Unlike traditional tools that rely on a static database of file signatures, the ADR Engine uses a Deep Learning Transformer Model trained on billions of data structures.
It doesn't just look for a file; it performs Semantic Verification. When our engine identifies a cluster of data, it evaluates its "probabilistic fit" within a larger file stream. This means Datile can now recover data from drives that have been partially overwritten or subjected to catastrophic system failures where every directory record has been wiped clean.
3. Professional Depth: "Digital Fingerprinting" Without Metadata
How does it work? Datile’s AI has been trained to recognize the "Digital Fingerprints" of different file types.
- The Heuristic Approach: Every file type (a JPEG, a 4K video, or a complex database) has a unique data entropy and distribution pattern.
- Pattern Recognition: Even if the "Metadata" (name, date, size) is gone, the AI analyzes the "Body" of the data. For example, it can recognize the specific mathematical frequency of a compressed pixel array in a photograph.
- The Reconstruction: The AI "predicts" the next missing fragment. If it finds a fragment of a high-resolution image, it scans the unallocated space for blocks that share the same "textural DNA," reassembling the image even if the fragments are scattered across thousands of non-contiguous sectors.
4. The AI Recovery Map: Possibilities and Challenges
While AI has opened new doors, the technical difficulty varies by data type. Datile is currently pushing the boundaries in the following areas:
| Data Type | AI Recovery Potential | Technical Challenge | Datile’s Current R&D Direction |
|---|---|---|---|
| High-Res Photos (JPG/HEIC) | High | Reconstructing color gradients across missing sectors. | Generative In-painting: Using AI to bridge microscopic gaps in corrupted image data. |
| Video Streams (MP4/MOV) | Medium-High | Maintaining frame-rate synchronization across fragmented GOP (Group of Pictures). | Temporal Alignment: AI-driven stitching of video frames based on motion-vector analysis. |
| Database Files (SQLite/SQL) | High | Rebuilding relational integrity between orphaned tables. | Structural Synthesis: AI-assisted re-indexing of fragmented database pages. |
| Encrypted Archives | Low-Medium | AI cannot bypass math; it requires the original key. | Key-Token Reconstruction: Using AI to find lost fragments of decryption tokens in RAM dumps. |
5. The Future: A World Without "Permanent" Loss
As we look toward the 2030s, Datile envisions a future where data loss is merely a temporary state of "disorganization" rather than a permanent tragedy.
We are moving toward Predictive Restoration, where your system, powered by Datile’s core technology, can detect early signs of NAND flash fatigue or file system instability before a crash even occurs. In this future, data recovery will be "invisible"—a background process of the Self-Healing File System.
The "Security Paradox" will find a new equilibrium. As encryption becomes more complex, AI will provide the bridge for legitimate users to navigate their digital estates with ease, ensuring that while the world becomes more secure, it does not become less accessible. Twenty-seven years ago, we began this journey with a single floppy disk. Today, we are building the neural pathways for the digital memory of tomorrow.
Conclusion: The Datile Promise
Through every era—from the mechanical hum of 1998 to the silent intelligence of 2026—Datile has remained the steady hand in the digital dark. We don't just recover data; we restore the continuity of your life’s work, your family’s memories, and your digital identity.
Datile: Heritage in Integrity. Future in Intelligence.
