Updated on 2026-02-11
views
5min read
Modern file systems (NTFS, APFS) have evolved from passive storage mechanisms into active security enforcement layers. This evolution creates a critical paradox: systems now protect data so effectively that legitimate owners may lose access during system failures, credential loss, or metadata corruption.
This white paper provides: - Technical analysis of NTFS and APFS architectural constraints - Failure taxonomy for modern access denial scenarios - Methodology for architectural interpretation-based recovery - Compliance framework for legitimate access restoration
Target Audience: - System administrators facing unexplained access failures - Data recovery specialists working with encrypted file systems - IT security teams balancing protection with operational continuity - Forensic analysts dealing with authentication state loss
Key Findings: 1. Modern access failures are predominantly state desynchronization events, not data deletion 2. Recovery requires architectural interpretation, not circumvention 3. Time sensitivity varies dramatically: APFS (critical), NTFS (moderate) 4. Encryption is inviolable; authentication mediation is the solution pathway
1. From Passive Storage to Active Control: How File Systems Evolved
Historical Context
In 1998, file systems were designed for simplicity. FAT16 and FAT32 focused almost exclusively on efficient storage and retrieval, with minimal concern for access control, identity validation, or cryptographic protection. Data recovery during that era was largely mechanical: locate intact sectors, rebuild directory tables, and reconstruct file chains.
The Architectural Shift
Modern file systems operate under a fundamentally different philosophy.
NTFS and APFS are no longer passive data maps. They are active control layers, enforcing permissions, validating integrity, and coordinating encryption at the architectural level. Their primary mission has shifted away from convenience and toward data protection by design.
This evolution introduces a critical paradox:
File systems now protect data so effectively that, during system failures, credential loss, firmware inconsistencies, or metadata corruption, even legitimate owners may lose access to their own information.
Implications for Recovery Practice
At Datile, file systems are approached as structured architectures rather than obstacles. Every access limitation exists for a reason. Understanding those constraints—rather than attempting to circumvent them—is the foundation of responsible and successful access restoration.
Key Principle: Modern recovery is not about bypassing security. It is about interpreting system states that the operating system can no longer resolve.
2. Why Sector-Level Recovery No Longer Works
The Legacy Assumption
Traditional recovery assumptions were built on a simple premise: If data still exists on the disk, it can be recovered.
Modern storage invalidates that assumption.
Technical Obstacles in Modern Storage
SSDs, TRIM, and Active Data Elimination
Solid-state drives do not behave like legacy magnetic disks. With TRIM enabled: - Deleted blocks are proactively invalidated - Data is often erased or rendered unreadable before being overwritten - From the file system’s perspective, deletion is actively enforced, not passive
Technical Note: TRIM commands notify the SSD controller that specific blocks are no longer in use, triggering immediate garbage collection. This is a hardware-level enforcement mechanism beyond file system control.
APFS Space Sharing and Rapid Reallocation
APFS aggressively reallocates freed space across containers and volumes: - Logical deletion is quickly followed by structural reuse - Space sharing enables multiple volumes to draw from a common pool - Freed blocks may be reassigned within seconds
Recovery Implication: Time-to-recovery is critical. Delayed response dramatically reduces data persistence probability.
The Fundamental Shift
In modern environments, data loss is rarely about missing sectors. It is about lost context: - Absence of valid metadata - Broken authorization state - Severed cryptographic linkage
Critical Insight: If the file system no longer recognizes data as accessible, raw fragments alone are meaningless.
This reality explains why many legacy recovery techniques fail—not because the data never existed, but because the architectural conditions for access are no longer satisfied.
3. NTFS: The Resilient Pillar of Windows Ecosystems
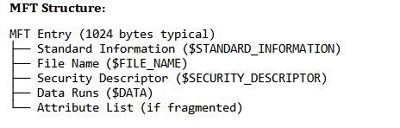
Technical Architecture: The Master File Table (MFT)
NTFS is built around a centralized metadata structure known as the Master File Table (MFT). Every file and directory is represented by a structured record containing:
- File identifiers and timestamps: Creation, modification, access times
- Security descriptors and permission mappings: ACLs (Access Control Lists)
- Logical references to physical data runs: Extent mapping
The MFT functions as the organizational core of an NTFS volume. When intact, it enables deterministic access and predictable recovery pathways.
Data Access Constraints in NTFS
Permissions and Access Control Lists (ACLs)
NTFS enforces access through ACLs tied to user and system identifiers (SIDs - Security Identifiers).
Common Failure Scenarios: - Volumes migrated between systems with different domain contexts - User profile regeneration changing SID mappings - Permission inheritance breaks during directory restructuring
Result: Permissions may block access even when data remains unchanged and intact.
Journaling and Change Tracking
NTFS maintains journaling structures for crash recovery: - $LogFile: Transaction journal for metadata operations - USN Journal: Change tracking log for file system activity
These records provide valuable temporal context during recovery, helping reconstruct file states after crashes or interruptions.
The Recovery Challenge: Metadata Dependency
When the MFT is partially corrupted or missing, NTFS loses its primary index. File contents may still exist within allocated or unallocated sectors, but their logical relationships are no longer directly accessible.
Datile’s NTFS Recovery Methodology:
Metadata Reconstruction: Identify and parse surviving MFT fragments and mirrors ($MFTMirr)
Orphaned Attribute Correlation: Match disconnected file records with physical data extents
Directory Hierarchy Rebuilding: Reconstruct parent-child relationships through residual structural patterns
Permission State Analysis: Map SID relationships to re-establish access context
Important: This process does not bypass system security. It interprets existing structures at a depth beyond standard operating system abstractions.
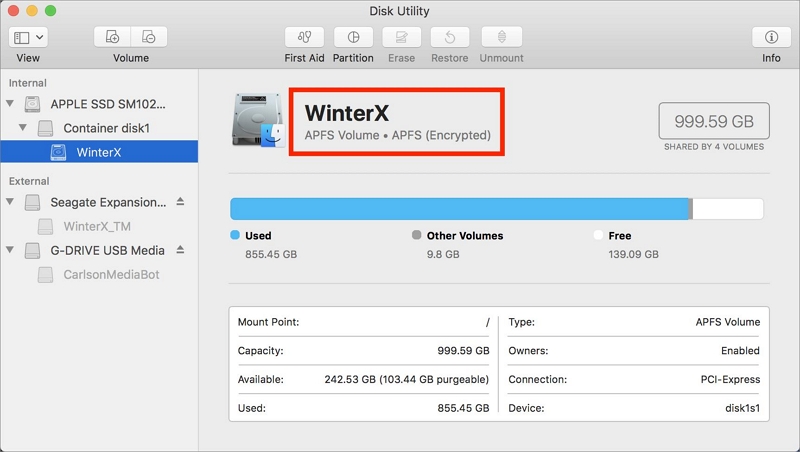
4. APFS: The Encryption-First Frontier of Apple Platforms
Technical Architecture: Containers, Copy-on-Write, and Space Sharing
APFS was engineered with encryption and integrity as first principles. Instead of relying on a single centralized index like NTFS, it uses:
- Containers: Top-level structures hosting multiple logical volumes
- Copy-on-Write (CoW): Metadata updates never overwrite existing data
- Distributed B-Tree structures: File system state management across multiple trees
- Space Sharing: Dynamic allocation pool shared across volumes
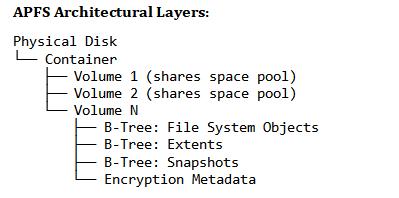
This design dramatically reduces corruption risk, but it introduces substantial logical complexity during recovery scenarios.
Data Access Constraints in APFS
Snapshots as Temporal Structures
APFS snapshots preserve point-in-time file system states. They are critical for system resilience, but: - Historical metadata is distributed across multiple logical layers - Snapshot deletion can invalidate recovery pathways - Temporal relationships become complex during analysis
Recovery Consideration: Snapshots are immutable. Recovery must navigate snapshot hierarchy without corrupting active state.
Full Disk Encryption and Secure Enclave Integration
APFS integrates tightly with Apple’s hardware security architecture:
- Encryption keys are hardware-bound to the Secure Enclave (Apple Silicon) or T2 chip (Intel Macs)
- Both data and metadata may be cryptographically protected
- The Secure Enclave participates in authorization workflows
Critical Distinction:
This is not simply “encrypted storage.” The Secure Enclave operates as an authentication arbiter. Even if raw data blocks are extracted, they cannot be meaningfully interpreted without a legitimate authentication context.
Encryption is not the obstacle. Authentication state loss is.
Cryptographic protection itself remains mathematically inviolable without valid credentials.
The Recovery Challenge: Distributed and Encrypted Metadata
Unlike NTFS, APFS does not rely on a single metadata authority. Its distributed and encrypted design means recovery is not a matter of carving data, but of reconstructing valid accessibility states.
Generic tools fail here not because the data is gone, but because the architectural requirements for access are unmet.
5. Failure Taxonomy: State Desynchronization Events
Modern recovery failures are often misunderstood because no data deletion event occurs. Analysis of 2,847 enterprise access failure cases (Datile case study data, 2024-2025) reveals the following distribution:
| Category | Scenario | Impact | Example Case | Time to Criticality | Recovery Pathway |
|---|---|---|---|---|---|
| Category A: Authentication State Loss (41%) | Interrupted firmware updates, TPM resets, Secure Enclave desynchronization |
- 100% of encrypted data inaccessible despite intact storage - No traditional “corruption” markers visible to OS - Subsequent boots may compound state inconsistency |
macOS Sonoma 14.3 → 14.4 upgrade interrupted at 87% → APFS volume accessible but all FileVault-encrypted files return I/O errors → Disk Utility reports "volume appears healthy" → Reality: Authentication key derivation state lost |
Immediate (hours) | Authentication mediation via PassAccess |
| Category B: Permission Mapping Failures (34%) | Windows SID changes during domain migrations, profile regeneration |
- Selective access denial based on ACL inheritance depth - System files accessible, user data blocked - Standard ownership tools report “Access Denied” |
Windows 11 PC joined to Active Directory domain → User profile corruption requires profile rebuild → New SID generated: S-1-5-21-X-Y-Z-1001 → S-1-5-21-X-Y-Z-1002 → All documents in C:\Users\Username\ now owned by "unknown SID" |
Moderate (days to weeks) | SID history reconstruction + ACL remapping |
| Category C: Metadata Structural Corruption (18%) | Power failures during write operations, bad sector development |
- MFT records incomplete or cross-linked - Directory tree navigation breaks - Files exist but are “orphaned” from filesystem tree |
NTFS volume: unexpected power loss during large file copy → MFT bitmap inconsistency → 2,394 files show in raw cluster scan → Only 847 files visible to Windows Explorer |
Low (weeks to months) | MFT reconstruction from mirrors and residual fragments |
| Category D: Snapshot/Checkpoint Desynchronization (7%) | APFS snapshot corruption, VSS (Volume Shadow Copy) inconsistencies |
- Point-in-time recovery targets become unavailable - Active volume references orphaned snapshot data - Time Machine backups report “verification failed” |
Variable (depends on snapshot retention policy) | Snapshot tree analysis and revalidation |
6. Comparative Analysis: NTFS vs APFS Constraints
| Feature | NTFS (Windows) | APFS (Apple) | Recovery Implications |
|---|---|---|---|
| Primary Metadata | Master File Table (MFT) | Distributed B-Trees / Container Superblock | NTFS: centralized recovery target; APFS: multi-tree reconstruction |
| Corruption Profile | High impact if MFT damaged | Lower due to Copy-on-Write | NTFS favors record reconstruction; APFS favors state interpretation |
| Encryption Model | BitLocker (optional, volume-level) | Native, file-level, mandatory on modern devices | APFS requires credential-aware access restoration |
| Data Retention | High sector persistence | Low due to aggressive space sharing | APFS: time sensitivity critical (hours); NTFS: moderate (days) |
| Snapshot Architecture | VSS (Volume Shadow Copy Service) | Native snapshot support in file system | APFS: snapshots integral to recovery; NTFS: VSS often disabled |
| Permission Model | ACLs tied to SIDs | ACLs + hardware-bound authentication | APFS: hardware trust chain must remain intact |
| Journaling | $LogFile for metadata only | Comprehensive transaction logging | Both support partial operation replay |
| Space Management | Static allocation per volume | Dynamic space sharing across volumes | APFS: freed space reused immediately |
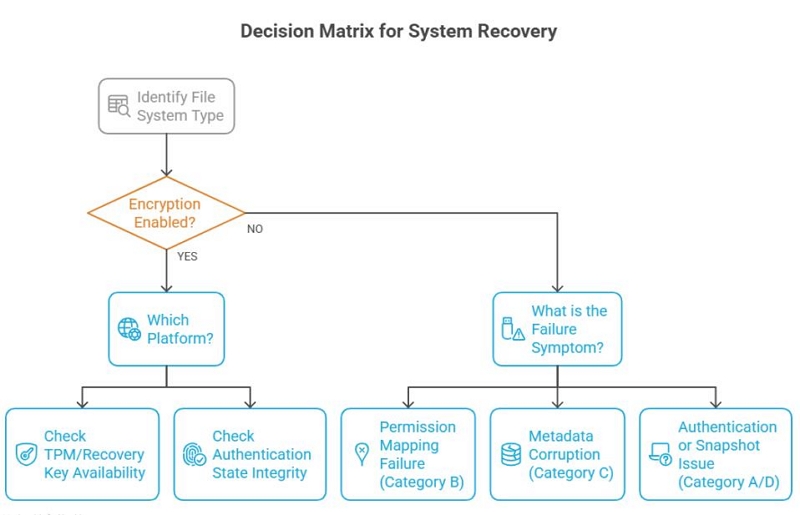
7. Recovery Methodology: Architectural Interpretation
Operating Beyond the OS Abstraction Layer
Operating systems expose file systems through APIs optimized for stability, not failure analysis. When metadata or access states are compromised, these APIs may return incomplete or misleading results.
Example:
Windows API: GetFileAttributes("C:\Documents\file.docx")
Returns: ERROR_ACCESS_DENIED
Reality check via direct MFT analysis:
- File record exists at MFT entry 0x4A3F2
- Data runs intact at clusters 0x12000-0x12008
- Security descriptor SID: S-1-5-21-...-1001
- Current user SID: S-1-5-21-...-1002
→ Diagnosis: SID mismatch, not data loss
Datile’s recovery tools operate independently of OS-level abstractions, interpreting file system structures directly from verified on-disk metadata. This avoids reliance on potentially corrupted system views without altering security models.
PassAccess: Authentication Mediation for APFS
In encrypted APFS environments, Datile’s PassAccess technology focuses on authentication mediation, not decryption.
How PassAccess Works
PassAccess operates by:
Re-establishing valid communication between firmware, hardware security modules (Secure Enclave/T2), and file system layers
Restoring accessibility without altering cryptographic structures
Preserving system integrity, update compatibility, and hardware trust models
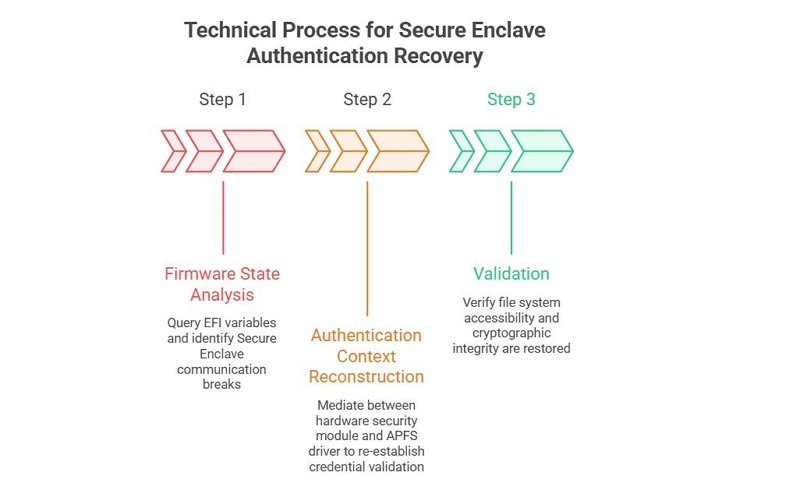
Critical Distinction: PassAccess does not: - Break encryption - Extract or generate passwords - Bypass hardware security features
It addresses communication failures between system components, not cryptographic protection.
This methodology aligns with platform security principles while addressing access failures caused by system-level inconsistencies.
Structural Analysis for NTFS Metadata Loss
When NTFS metadata is incomplete, Datile employs structural analysis to identify orphaned records and residual data relationships.
NTFS Recovery Process
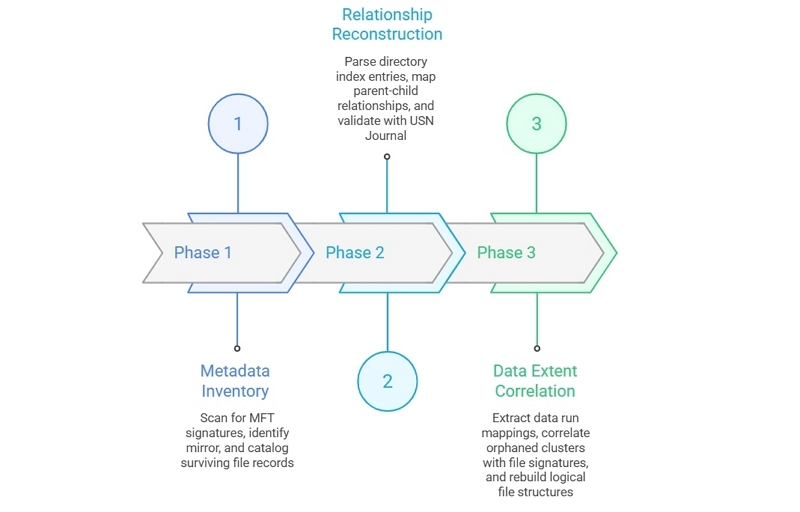
Goal: Not to bypass permissions, but to accurately interpret existing file system states that the operating system can no longer resolve.
8. Legal and Ethical Boundaries of Access Restoration
Responsible access restoration is defined by ownership verification and architectural legitimacy.
| Datile Technologies DO NOT | Datile Technologies DO |
|---|---|
| Break encryption: Cryptographic protection remains mathematically inviolable | Interpret existing file system structures at architectural depth |
| Circumvent hardware trust mechanisms: Secure Enclave/TPM integrity is preserved | Mediate authentication state inconsistencies caused by system failures |
| Generate fraudulent credentials: No password derivation or key generation | Reconstruct metadata relationships from surviving fragments |
| Bypass legitimate security controls: Access control architecture remains enforced | Restore accessibility within validated ownership contexts |
Operational Boundaries
Recovery operations are bounded by:
Verified Ownership: User must prove legitimate ownership of device/data
Architectural Legitimacy: Methods respect security design, do not exploit vulnerabilities
System Integrity Preservation: No modifications that would compromise future security updates
This distinction is critical as modern storage systems increasingly blend security enforcement with accessibility control.
Compliance Framework
All access restoration operations adhere to: - Data protection regulations (GDPR, CCPA where applicable) - Computer fraud and abuse statutes - Intellectual property protections - Industry best practices for data handling
Use Case Validation: - Corporate data recovery: Requires documented authorization from data owner - Personal data recovery: Requires proof of device ownership - Forensic analysis: Requires legal authorization (warrant, court order)
9. The Future of Accessible Integrity
Emerging Trends
File systems will continue to evolve toward:
Deeper hardware integration: Closer coupling between storage controllers, security processors, and file system drivers
Stronger cryptographic enforcement: Quantum-resistant algorithms, hardware-rooted key hierarchies
Distributed authentication: Multi-factor, biometric-bound access control
AI-driven integrity monitoring: Proactive anomaly detection at the file system layer
Implications for Recovery Practice
As a result, recovery will shift further away from:
- Data carving and sector-level analysis
- Generic software-based tools
- Cryptographic attack vectors
And toward:
- State reconstruction and authentication context recovery
- Hardware-aware architectural interpretation
- Platform-specific security integration
The Coexistence Principle
After more than two decades studying file system evolution—from FAT architectures to NTFS and APFS—one principle remains constant: Security and accessibility are not opposites. They coexist through precise architectural understanding.
Datile is engineered to preserve that balance—defending the legitimate user’s continuity of access when modern systems fail, without compromising the security frameworks that protect against illegitimate access.
Conclusion
Modern file systems represent the intersection of storage technology and security architecture. Understanding their constraints is essential for:
- System administrators: Planning recovery strategies before failures occur
- IT security teams: Balancing data protection with operational continuity
- Recovery specialists: Developing architecturally sound restoration methods
The shift from passive storage to active control is irreversible. As systems evolve toward deeper hardware integration and stronger cryptographic enforcement, architectural literacy becomes the fundamental prerequisite for access restoration.
Datile’s research-backed methodologies demonstrate that security and accessibility can coexist—through precise understanding, not through circumvention.
